This is going to be a short one, because so much has been written on this, and the level of (in)competence exhibited by so many people around this has almost driven me crazy.
Yes, the Sony hack. Not going to comment on what has been done, what should have been done, the sophistication of the attack, the ability to detect tens of terrabytes leaving a network, or the way to handle this (technically, politically, diplomatically, business, ugh – you name it…).
But I do find it ironic that this post comes right after my previous one, now aptly titled “To the full extent of their capabilities” by Dave Aitel (who’s also had his share of commenting on the Sony hack).
I was vocal enough around this, especially (and weirdly I must say) as someone who suddenly sounds like the responsible adult, urging for deeper and more comprehensive forensic work and not knee-jerk attribution. Attribution, as we all (should) know, is difficult. Especially in the “cyber” realm, where fingerprints are more difficult to link to actors, who are in turn difficult to link to aggressors.
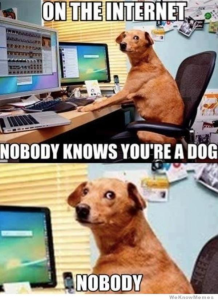 On the Internet, everyone can be anyone, and planting false flags is common practice among even the less capable threat actors. Acting on such red herrings is not only irresponsible, it can also be dangerous (an “unnamed official” at the Pentagon responded as such to the DDoS attacks on July 4th 2009). And it looks like we are facing the same weak evidence again. I highly recommend reading Fauxtribution by Krypt3ia, who really lays out the evidence, and the highly speculative nature of the attribution from the FBI on this one.
On the Internet, everyone can be anyone, and planting false flags is common practice among even the less capable threat actors. Acting on such red herrings is not only irresponsible, it can also be dangerous (an “unnamed official” at the Pentagon responded as such to the DDoS attacks on July 4th 2009). And it looks like we are facing the same weak evidence again. I highly recommend reading Fauxtribution by Krypt3ia, who really lays out the evidence, and the highly speculative nature of the attribution from the FBI on this one.
Looking at TTPs (Tools, Tactics, and Procedures) only in order to derive attribution is not enough. Without being to link real activities to a human actor, and follow up with a more “traditional” investigation (motivation, funding, accessibility, relationships), TTPs and other forensic evidence leaves us with a highly biased view of what’s going on. More worryingly, this view is almost entirely controlled by the real attacker, who had the time and opportunity to choose who would they like to appear as at the end of the day when the attack is discovered. Having clear documentation on TTPs for almost any major actor, with highly accessible online resources such as proxies, compromised hosts, and for-rent bots/servers, and finally throw in some foreign language references, and we have ourselves a perfectly guised threat actor.
Unless the investigation ends up with a multi-national cooperative law enforcement effort, enforced by the legal systems, and commercial capabilities, this goose chase isn’t going to end well. We can (gulp) take a hint from Microsoft’s playbook and their recent endeavors in hunting down the true sources of mass botnets and malware attacks. One can only hope…
Leave a Reply